Dallas CISO Community
Executive Summit
November 15, 2023 | Renaissance Dallas Richardson Hotel
November 15, 2023
Renaissance Dallas Richardson Hotel
Collaborate with your peers
Get together with Dallas's top CISOs to tackle shared business challenges and critical priorities facing your role today. Participate in this one-day, local program with peer-driven topics and interactive discussions with your true C-level peers.
Join your peers to discuss the most critical issues impacting CISOs today:
Quantifying the business's cyber-risk appetite and leveraging it to frame security investments
Focusing on the entire CISO lifespan - from position acceptance to potential paths that lie ahead
Anticipating the trajectory of tech advancements and adopting a protocol on behalf of the business
Dallas CISO Governing Body
The Governing Body Co-Chairs shape the summit agenda, ensuring that all content is driven By CISOs, For CISOs®.
Governing Body Co-Chairs

Sara Andrews
Experian
Global CISO

David Bell
American Airlines
Managing Director, Information Security & Technology Risk Management & Chief Information Security Officer

Patrick Benoit
Brinks
CISO
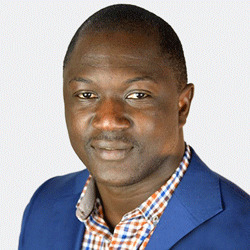
Mustapha Kebbeh
Ultimate Kronos Group
Chief Security Officer

Scot Miller
Mr. Cooper
SVP, CISO

Scott Moser
Sabre Corporation
SVP, Chief Information Security Officer

Harold Rivas
Trellix
SVP & CISO

Shamoun Siddiqui
Neiman Marcus
VP, CISO

Gary Toretti
CBRE
SVP, Chief Information Security Officer
What to Expect
Agenda
7:45am - 8:30am Registration & Breakfast
8:30am - 9:15am Keynote
The Magic of Empathetic Leadership

Nash Fung
Keynote Speaker | Magician
More than 15 years of experience as a crisis line volunteer taught Nash Fung the value of empathy and how it can be used to empower others. Now, using his background as a magician, he’s passing those communication techniques on to you.
Join this magical, interactive keynote as Fung shares:
- The importance of leading with empathy and authenticity
- How to ensure your teammates feel heard, understood and valued
- How empathy leads to empowerment
9:15am - 9:40am Networking Break
9:40am - 10:25am Breakout Session
The Path to Alignment – The CIO and CISO Relationship

Patrick Benoit
CISO
Brinks

Mike Santimaw
SVP, Chief Digital Officer
Mode Global
CIO-CISO partnerships are built on trust and thrive when leaders invest in each other throughout the organization. When the goals of each executive do not align, a cohesive approach becomes crucial. A well-disciplined, integrated and communicative strategy can help to avoid program failures and vulnerabilities, safeguarding both systems and the business.
Join this session to explore how to:
- Overcome communication challenges and competing priorities
- Ensure security is represented as a holistic element of the organization
- Strengthen the IT-Security partnership to fuel innovation and accelerate new technology deployments
9:40am - 10:25am Breakout Session
Keeping it Simple - Breaking Down Cloud Misconfigurations
Hosted by Qualys

Josh Hankins
Chief Technical Security Officer (CTSO) - Americas
Qualys
Monitoring, alerting, immutable configurations are simple strategies that lead to security success. But why are we our own worst enemy?
Join this Jonathan Trull, CISO at Qualys in this session to dig in deeper on:
- The persistent issues of insecure configurations such as IAM, alerting, monitoring logging and encryption
- Misconfigurations that are consistently exploited in the real world
- The why AND how to addressing all of the above
9:40am - 10:25am Executive Boardroom
Crisis Planning – Flip the Asymmetry with Attackers
Hosted by Sygnia

Marty Ray
CISO
Fossil

Nats Elluri
Director, Cyber Security
United Surgical Partners International

Avi Sambira
Director, Client Leadership | NA
Sygnia
Preparing for a cyber crisis is imperative and can determine whether it becomes a major catastrophe or a manageable incident. Whether you have experience navigating a crisis or are preparing for the inevitable attack to come, come together with your peers to leverage the wisdom in the room to tackle complex challenges and get ahead of the attackers.
Join this session to discuss:
- Evaluating common options, dilemmas, and pitfalls in crisis planning
- Understanding the impact of technical and stakeholder management decisions on the business
- Identifying key gaps and vulnerabilities often overlooked by security teams
9:40am - 10:25am Executive Boardroom
Cut Through the Noise - Protect Against Emerging Threat Vectors That Matter
Hosted by Akamai

Anthony (Tony) Lauro
Director, Security Technology and Strategy
Akamai Technologies

Glen Armes
Chief Information Security Officer
Old Republic International Corporation

Royce Holden
AVP, Technology Security & Compliance, CISO
Dallas/Fort Worth International Airport
Organizations face an infinite number of potential threats as they pursue digital transformations and criminals evolve their attack techniques. While there are certain threats – malware, phishing, credential abuse, etc - that remain top trends year after year, there are always new threat vectors emerging. Since even the most well-funded organizations cannot address all threats, how can CISOs differentiate between what is emerging and dangerous and what is overhyped and a distraction?
Join this session to discuss:
- Analyzing today’s emerging threat vectors to determine relevance and urgency
- Contextualizing new threats within your detection and response protocols
- Baselining your security posture and boosting resilience with multiple layers of defense
10:25am - 11:00am Networking Break
10:30am - 10:55am Peer-to-Peer Meetings
Peer-to-Peer Meetings
Connect with like-minded peers in a one-on-one setting through Evanta’s Peer-to-Peer Meetings. You will be matched with peers in your community based on your shared interests and priorities.
11:00am - 11:45am Breakout Session
From the SEC to the Boardroom - The Evolving Nature of Cyber Risk
Hosted by Zscaler

Sanjit Ganguli
CTO-in-Residence
Zscaler
Becoming a cyber-resilient organization requires risk ownership and responsibilities to be expanded across the C-suite and board, changing the way that cybersecurity challenges are addressed at all levels of the organization. This has been complicated by a recent SEC ruling requiring US public companies to publicly disclose “material breaches’. CISOs need to embrace zero trust security and adjust their board engagement approach to get the appropriate level of support and guidance on cybersecurity initiatives.
In this session, we will discuss how executives can increase cyber and business resilience with board buy-in and how to:
- Gain confidence on cybersecurity oversight and forward direction, including messaging to the board
- Articulate cyber risk posture, controls, and mitigation strategies in place, with board-level terminology and understand the dealing with new SEC rulings
- Learn how zero trust architecture secures users, workloads, and IoT/OT devices by addressing critical security shortcomings of routable networks
11:00am - 11:45am Breakout Session
GRC for a Changing World — Adaptation and Resilience

Sonja Hammond
VP, CISO
National Veterinary Associates
Having a secure data governance program that successfully aligns with business priorities and compliance is unparalleled. As data becomes increasingly available across multiple cloud environments, it's critically important to preserve the confidentiality, integrity, and availability of information. CISOs must establish a secure, modern framework that protects high quality data throughout its lifecycle.
Join this session to discover:
- Aligning technology, process and operations to improve governance across a complex organization
- Where the challenges and roadblocks lie, including privacy concerns & compliance issues
- Lessons learned from implementation and operation
11:00am - 11:45am Executive Boardroom
Strategic Pitfalls in Third-Party Risk Management
Hosted by RiskRecon, a Mastercard Company

Dewakar Garg
Sr. Director of Information Security & Compliance
Mavenir

Syam Maddimsetty
Director, Information Security and Compliance
Overhead Door

Neal Roylance
Director of Security Research
RiskRecon - A MasterCard Company
Managing cyber risk across an enterprise IT infrastructure has never been harder. Remote workers, advancing attack methods, and an ever-expanding vendor network are challenging every firm, as total visibility into threats has become nearly impossible. As digital business strategy matures, more organizations are becoming dependent on the cyber posture and protection of third parties. Third-party risks present a unique challenge because you are depending on vendors and partners to operate securely to keep your data and information safe. How are you mitigating the associated risks and demonstrating this to the business to ensure effective security programs?
Join our session to hear about:
- Common failings across TPRM programs that led to breach events
- How executives can provide strategic direction for third-party risk teams
- Key practices being implemented by leading vendor risk firms to maintain strong supply chain risk management
11:00am - 11:45am Executive Boardroom
The Most Important Shift for Cybersecurity in a Generation
Hosted by Netskope

Robert Pace
VP, CISO
Invitation Homes LP

Scott Moser
SVP, Chief Information Security Officer
Sabre Corporation

James Robinson
Deputy CISO
Netskope
We live in a world where everything is hybrid and the blend between personal, corporate, private and public is ever-changing and presents us with a host of new challenges. This has increased and complicated the attack surface and the pressure to converge tools and do “more with less” is at peak levels. We must meet this watershed moment with the right team, plans, and technology.
Join this interactive session to learn:
- How to build an effective plan for change without adding to the chaos
- What consolidation approaches save money without sacrificing security
- Use cases that deliver immediate value and efficiency while improving user experience
11:45am - 12:15pm Networking
Rising Together — Empowered Women, Empower Women

Sara Andrews
Global CISO
Experian

Brandi Johnson
Deputy CISO
Toyota Financial Savings Bank

Carol Weaver
Director, Technology and Information Security Risk Management
Texas Capital Bank
This will be an intimate, informal space for women in leadership roles and their allies to freely discuss best practices, key challenges, and mission-critical priorities. Come prepared to share ideas and forge new connections that can help empower each other to make an impact in your organizations and communities.
This session is aimed at, but not limited to, women who are leading at their organizations (C-Level or equivalent) and those reporting directly to the C-Level/equivalent. Priority access will be reserved for these groups.
11:45am - 12:30pm Lunch Service
Apply to Participate
Apply to participate in the Dallas CISO Community Executive Summit.
Gartner facilitates exclusive, C-level communities by personally qualifying and understanding the priorities, challenges and interests of each member.
Our selective approach maintains the high quality of the network and ensures top-level discussions with peers from the world’s leading organizations.
Each application will be reviewed, and once your participation is confirmed, you will have access to year-round community programs.
Location
Venue & Accommodation
Renaissance Dallas Richardson HotelParking
On-site parking rate is $15/day $20 for Valet
A block of rooms has been reserved at the Renaissance Dallas Richardson Hotel at a reduced conference rate. Reservations should be made online or by calling 972/367/2000. Please mention Dallas Executive Summit to ensure the appropriate room rate.
Deadline to book using the discounted room rate of $149 USD (plus tax) is October 23, 2023.
Community Program Manager
For inquiries related to this community, please reach out to your dedicated contact.























