Dallas CISO Community
Inner Circle
September 2, 2026 | The Constellation Club
September 2, 2026
The Constellation Club
Collaborate with your peers
Join Dallas's top CISOs for an intimate networking dinner and facilitated discussion on key business challenges. Enjoy a relaxed evening of dinner and drinks with your peers to share best practices, make new connections and build professional relationships.
Join your peers to discuss the most critical issues impacting CISOs today:
Strengthening Security Posture Amid Evolving and Unpredictable Threats
Focusing Cyber Resilience for Critical Operations
Balancing GenAI Innovation with Practical Governance
Dallas CISO Governing Body
The Governing Body Co-Chairs shape the discussion topics and agenda, ensuring that all content is driven By CISOs, For CISOs®.
Governing Body Co-Chairs

David Bell
CBRE
SVP, CISO
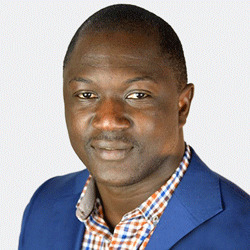
Mustapha Kebbeh
UKG
VP & Chief Security Officer

Scot Miller
Mr. Cooper
SVP, Chief Information Security Officer

Scott Moser
Sabre Corporation
SVP & CISO

Becky Palmer
National Life Group
VP & CISO
Agenda
Coming Soon
We are currently working with C-level leaders in your community to build the most timely and relevant agenda. All of our sessions, topics and discussions are driven By CISOs, For CISOs® to ensure the most valuable experience.
Apply to Participate
Apply to participate in the Dallas CISO Community Inner Circle.
Gartner facilitates exclusive, C-level communities by personally qualifying and understanding the priorities, challenges and interests of each member.
Our selective approach maintains the high quality of the network and ensures top-level discussions with peers from the world’s leading organizations.
Each application will be reviewed, and once your participation is confirmed, you will have access to year-round community programs.
Location
Venue
The Constellation ClubCommunity Program Manager
For inquiries related to this community, please reach out to your dedicated contact.







